Browser fingerprinting: what it is and how to reduce it
TL;DR
- Browser fingerprinting collects your device and browser settings to create a unique identifier that tracks you across the web
- Unlike cookies, fingerprints are persistent and cannot be easily deleted or blocked by standard privacy tools
- A VPN hides your IP address but does not stop browser fingerprinting, as the tracking relies on your device configuration
- Techniques like canvas fingerprinting and font enumeration exploit standard web features to gather highly specific data
- You can reduce your fingerprint by using privacy-focused browsers, standardizing your settings, and avoiding unique extensions
What a VPN Does (and Doesn't)
✅ A VPN does: - Encrypts your connection between your device and the VPN server - Hides your IP address from websites and trackers - Helps reduce exposure on public networks - Changes your apparent location by routing traffic through a server
❌ A VPN doesn't: - Stop browser fingerprinting or script-based tracking - Block cookies or tracking pixels - Make you completely anonymous online - Prevent websites from identifying you if you log into an account
You clear your cookies, use private browsing mode, and connect to a VPN. You might think you've stopped websites from tracking you. But there's a more persistent, invisible method that doesn't rely on storing files on your device: browser fingerprinting.
Instead of leaving a tracker on your computer, websites look at the unique characteristics of your device and browser. By combining dozens of seemingly harmless settings—like your screen resolution, installed fonts, and graphics hardware—they can identify you with startling accuracy.
This guide explains how browser fingerprinting works, why it's so difficult to stop, and the practical steps you can take to blend in with the crowd.
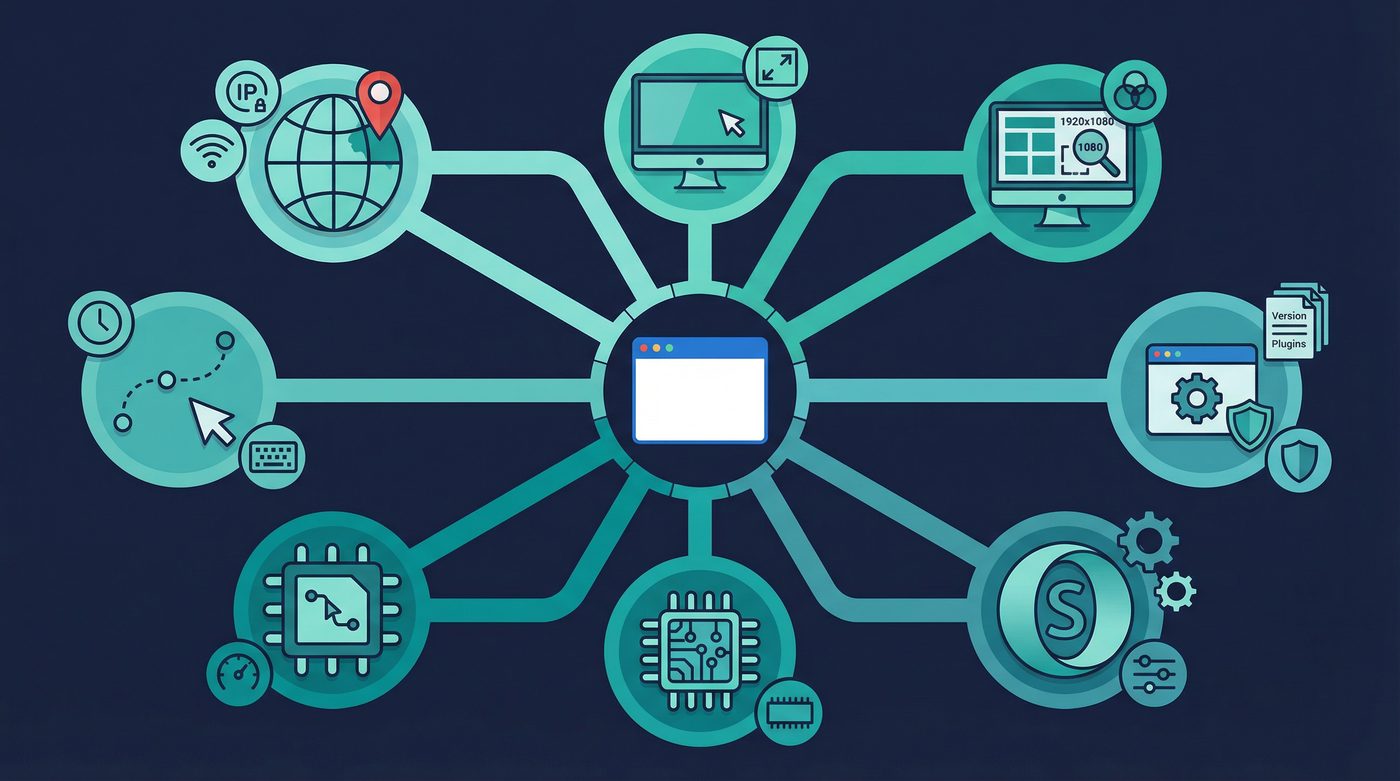
How Fingerprinting Works: The Data Collected
When you visit a website, your browser automatically shares information to ensure the page loads correctly. Fingerprinting scripts harvest this data to build a profile. The more unique your setup, the easier you are to identify.
Here is the data typically collected:
- Screen & display: Resolution, color depth, and whether you use multiple monitors.
- Browser details: User agent string (browser version and OS), supported languages, and installed plugins.
- System config: Time zone, CPU architecture, and device memory.
- Graphics & hardware: Information about your graphics card (GPU) and how it renders images.
- Behavioral signals: How you move your mouse, typing speed, and scrolling patterns.
- Network & location: Local IP addresses (via WebRTC leaks) and network connection type.
Individually, none of these data points identify you. Millions of people use the same browser version. But when combined, they create a highly specific identifier.
Why Fingerprinting is So Effective
Combinatorial Rarity
Fingerprinting relies on probability. If 1 in 20 people use your specific browser version, 1 in 50 use your screen resolution, and 1 in 100 have your exact list of installed fonts, the combination of those three traits alone makes you 1 in 100,000. Add a dozen more data points, and your fingerprint becomes entirely unique.
Persistence and Difficulty to Detect
Unlike cookies, which you can view and delete, fingerprinting happens invisibly in the background. It uses standard web technologies (like JavaScript and HTML5) that are required for most modern websites to function. Because it doesn't store anything on your device, there is nothing to clear or block using traditional methods.
Cross-Site Tracking
Once a fingerprint is generated, it can be shared across different websites by third-party tracking networks. Even if you change your IP address or use private browsing mode, your device's hardware and software configuration remains the same, allowing trackers to link your activity across the web.
Why VPNs Don't Stop Fingerprinting
A VPN is a critical tool for network privacy, but it operates at a different layer than browser fingerprinting.
When you use a VPN, your IP address changes, and your traffic is encrypted. However, the fingerprinting scripts run inside your browser. They still have access to your screen resolution, installed fonts, and hardware details.
A VPN changes where your traffic appears to come from, but it doesn't change what your device looks like to the website. To combat fingerprinting, you need tools that alter or standardize the data your browser reveals.
Learn more: Do VPNs make you anonymous? What a VPN can and can't hide
5 Common Fingerprinting Techniques
Trackers use various methods to extract data from your device. Here are the most common techniques:
1. Canvas Fingerprinting
How it works: The website instructs your browser to draw a hidden image or text using the HTML5 Canvas element. Because different graphics cards, drivers, and operating systems render images slightly differently at the pixel level, the resulting image is unique to your hardware. Invasiveness: High. It silently extracts hardware-level details without requiring any permissions. How to block it: Privacy-focused browsers can block canvas data extraction or add random noise to the rendered image, changing the fingerprint every time.
2. WebGL Fingerprinting
How it works: Similar to canvas fingerprinting, WebGL is used to render 3D graphics in the browser. Trackers use it to identify your specific graphics card model and its rendering capabilities. Invasiveness: High. It provides highly specific hardware identifiers. How to block it: Disabling WebGL or using a browser that restricts WebGL access prevents this data collection.
3. AudioContext Fingerprinting
How it works: The browser is instructed to process a short audio signal. Differences in your device's audio hardware and software stack cause minute variations in the output, which are measured to create an identifier. Invasiveness: Medium. It relies on hardware differences but is less commonly used than canvas fingerprinting. How to block it: Browsers like Brave and Tor block or spoof AudioContext requests by default.
4. Font Enumeration
How it works: Trackers use JavaScript or CSS to check which fonts are installed on your system. A unique combination of custom or obscure fonts makes your device stand out. Invasiveness: High. The list of installed fonts is often highly unique to individual users. How to block it: Restrict the browser to only use standard, pre-installed system fonts.
5. Behavioral Fingerprinting
How it works: Trackers monitor how you interact with the page—mouse movements, click patterns, and typing speed. Invasiveness: Medium. It requires active interaction and is often used for bot detection, but can be used for tracking. How to block it: Difficult to block entirely without breaking website functionality, but disabling JavaScript stops most behavioral tracking.
6 Strategies to Reduce Your Fingerprint
The goal of anti-fingerprinting isn't to hide your data entirely—that often breaks websites. Instead, the goal is to blend in. You want your browser to look exactly like millions of others.
1. Use a Privacy-Focused Browser
Standard browsers like Chrome are designed to share data. Switch to a browser built for privacy: - Tor Browser: The gold standard for anti-fingerprinting. It standardizes every setting so all Tor users look identical. - Brave: Includes built-in fingerprinting protection that randomizes data (like canvas and audio outputs) so your fingerprint changes constantly. - Firefox: Offers strong anti-fingerprinting features, but they must be manually enabled in the settings.
2. Disable JavaScript on High-Risk Sites
Most fingerprinting techniques rely on JavaScript. Disabling it completely stops fingerprinting, but it also breaks many modern websites. Use extensions like NoScript to selectively allow JavaScript only on trusted sites.
3. Avoid Unique Browser Extensions
Every extension you install changes your browser's behavior slightly, making you more unique. Stick to a few essential, widely used extensions (like uBlock Origin) and avoid obscure add-ons.
4. Use Standard Screen Resolutions
If you resize your browser window to a custom dimension, that exact pixel count becomes part of your fingerprint. Keep your browser maximized or use standard resolutions to blend in.
5. Disable WebRTC
WebRTC is a technology used for real-time communication (like video calls), but it can leak your real local IP address even if you're using a VPN. Disable WebRTC in your browser settings or use an extension to block it.
Learn more: VPN leaks explained: DNS, IPv6, and WebRTC, and how to check yours
6. Clear Site Data Regularly
While fingerprinting doesn't rely on cookies, trackers often use both methods together. Clearing your cookies and site data regularly prevents trackers from linking your old fingerprint to a new session.
Learn more: Tracking 101: cookies, pixels, device IDs, and where a VPN fits
The PrivateByRight Approach
We build tools to protect your network traffic, but we are honest about the limits of a VPN. A VPN encrypts your connection and hides your IP address, but it cannot stop browser fingerprinting.
Privacy requires a layered approach. We recommend combining PrivateByRight VPN with a privacy-focused browser, tracker blockers, and good digital hygiene. Our systems are designed to minimize data collection at the network level, ensuring that your connection data is never logged or stored.
Learn more: Our privacy principles: data minimisation, default protection, and clarity
FAQs
Can I completely stop browser fingerprinting?
No. If you block all data collection, most modern websites will refuse to load or function correctly. The goal is to reduce your uniqueness by standardizing your browser settings so you blend in with millions of other users.
Does incognito mode stop fingerprinting?
No. Incognito or private browsing mode only deletes cookies and history after you close the window. It does not change your browser fingerprint or stop scripts from collecting hardware data during your session.
Why do websites use fingerprinting instead of cookies?
Cookies are easy for users to view, block, and delete. Fingerprinting is invisible, persistent, and operates using standard web technologies that are difficult to block without breaking the website.
Is browser fingerprinting legal?
In many jurisdictions, fingerprinting is subject to the same regulations as cookies (such as the GDPR in Europe), requiring user consent. However, enforcement is difficult because fingerprinting is hard to detect and prove.
Does a VPN help with fingerprinting at all?
A VPN hides your IP address, which is one data point used in fingerprinting. However, it does not stop the collection of hardware and software data. You need a VPN for network privacy and a secure browser for device privacy.
Learn more: What is a VPN? How it works and what it does (in plain English)
Sources & Further Reading
- Electronic Frontier Foundation (EFF). (2023). Cover Your Tracks: How Trackers See Your Browser.
- Laperdrix, P., et al. (2020). Browser Fingerprinting: A Survey. ACM Transactions on the Web.
- Mozilla Foundation. (2024). Firefox Privacy and Anti-Fingerprinting Documentation.
- Brave Software. (2023). Fingerprinting Defenses in the Brave Browser.
- Tor Project. (2024). Tor Browser Design and Anti-Fingerprinting Strategies.
Related Guides
- Learn more: Tracking 101: cookies, pixels, device IDs, and where a VPN fits
- Learn more: Do VPNs make you anonymous? What a VPN can and can't hide
- Learn more: What is a VPN? How it works and what it does (in plain English)
- Learn more: VPN leaks explained: DNS, IPv6, and WebRTC, and how to check yours
- Learn more: Metadata vs content: why who, when, where can matter as much as what
- Learn more: Our privacy principles: data minimisation, default protection, and clarity

